Choose Olvid Enterprise
for its security.
Keep it
for its simplicity.
Get unparalleled security for all your internal and external communications, without ever compromising any data, and continue your communications even in case of a cyber attack.
Internal communication
Protect communications between your employees, with an unprecedented security level.
Olvid is not just for the elite. Make no mistake, data leaks affect all levels in the enterprise.
External Communications
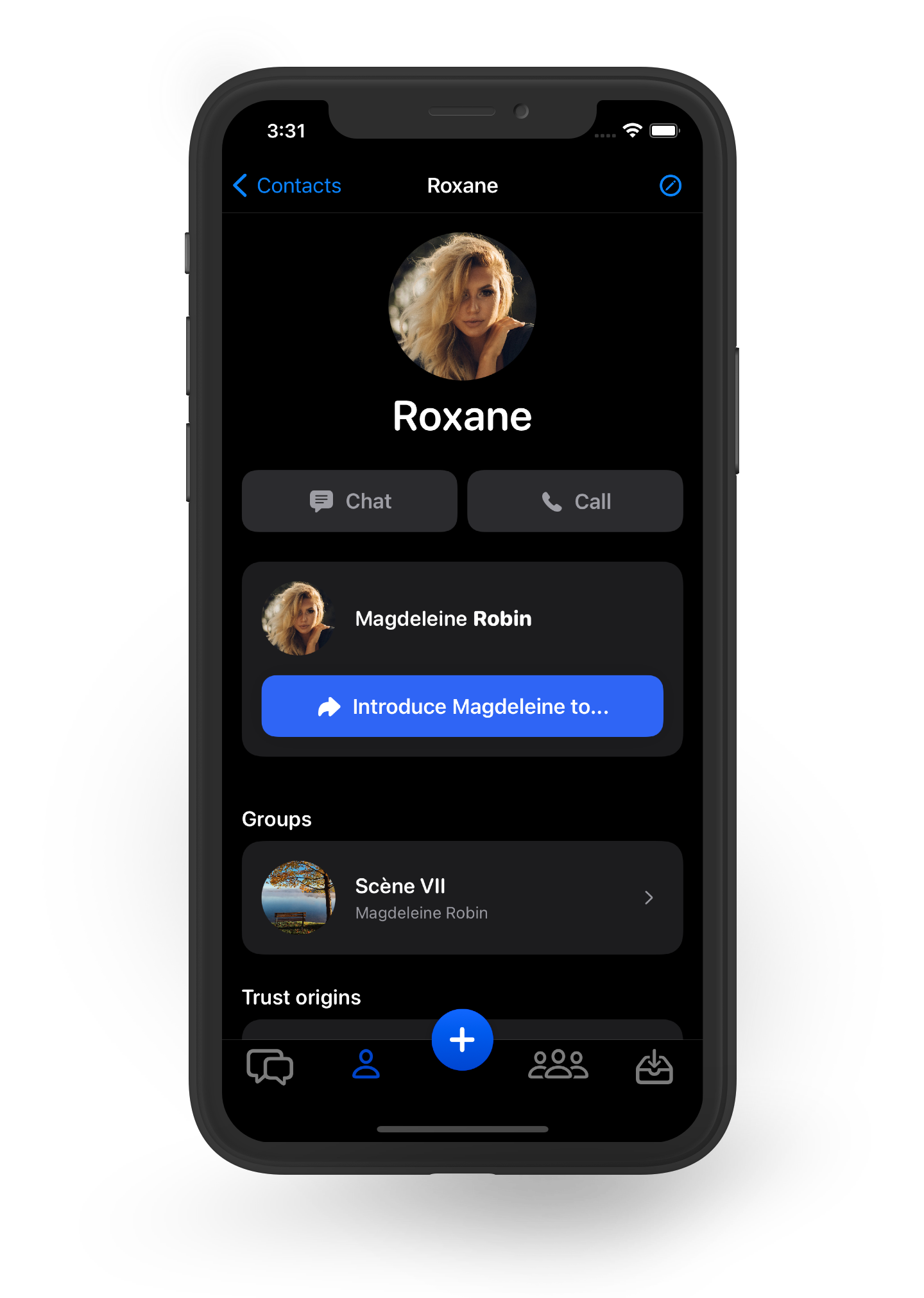
Olvid Enterprise is fully compatible with the free version and allows your employees to communicate with any other user, even if they are not part of your company.
Establishing a secure communication channel only takes seconds, without any impact on your information system.
Cyber-resilience
Because Olvid's security is completely decentralized, your employees can resume communication, even in case of a cyber attack.
Olvid is the ideal solution for your Business Continuity Plan.
Your Enterprise features
While taking advantage of all the free features, Olvid Enterprise allows for easy and secure deployment and ensures a simple and intuitive user experience.
Secure calls
Enjoy secure calls, with one or more people. Just like messages, calls are end-to-end encrypted and no one can eavesdrop on your conversations.
You no longer need to travel in person to deal with sensitive issues!
Simplified management
Make license management easy via the Olvid Management Console.
Create and activate licenses based on your needs and missions.
Create discussion groups reflecting your governance and organizational charts.
Automated deployment
Simplify enrollment within the company (add contacts in one click), based on your existing authentication mechanisms, and distribute Olvid via an MDM.
Immediate remediation
If one of your employees' phone is lost or stolen, instantly and automatically revoke his keys and secure channels directly from the Olvid Management Console.
Solve your security issues
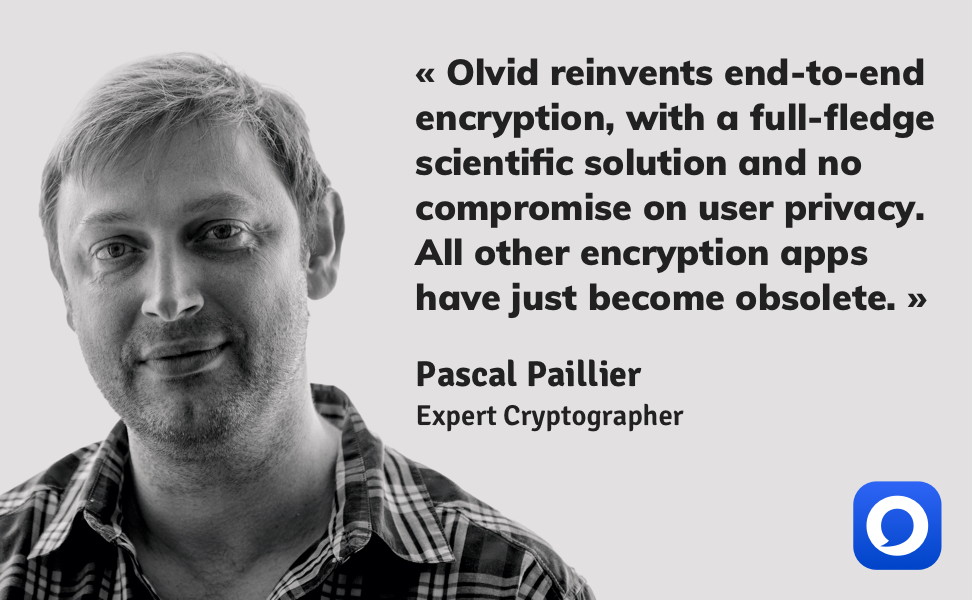
Olvid allows to mathematically prove the impossibility for a third party to learn anything about your communications.
Keep control of digital identities
Olvid allows you to create your own contact list by simply verifying the identity of each of your contacts yourself, or by using your own authentication methods.
Protect data by complying with the GDPR
Olvid does not need any personal data to operate: no phone number, no email, no name. Just nothing. By design, Olvid is 100% GDPR compliant.
Fight against shadow IT
It's no secret: supposedly free tools from the private sphere are massively used in a professional context.
By choosing Olvid, you fight against shadow IT by finally offering a secure messaging solution that is as simple as consumer tools, and you protect your company from those solutions financed by your data exploitation.
Free yourself from foreign solutions subject to extra-territorial laws
Most solutions may be required to provide data about your communications, even if their servers are located in Europe. This is the case, for example, with software suites subject to the Cloud Act. Do you want all your data available to them in the clear?
Olvid's unique security model prevents access to your data. Even if the servers are compromised.
How to choose
your communication tool?
What are the right questions to ask yourself when you have to choose your communication tools? Here we offer some evaluation criteria to compare the security level of instant messengers.
Where is the data stored?
Is the data stored on servers subject to extra-territorial laws (such as the Cloud Act), on a sovereign cloud, on premise or on device?
How is the data encrypted and who holds the keys?
Disk encryption, password encryption or user key encryption?
How do you access the data?
Access with login & password, multi-factor authentication, web application or dedicated & cryptographic application?
Testimonials